Crypto’s Most Infamous Wallet Drains: Key Cases and Lessons for Securing Your Assets

The growth of digital finance has brought immense opportunity, but it has also attracted sophisticated cybercriminals who exploit vulnerabilities to drain crypto wallets. Over the years, several wallet-draining cases have highlighted the devastating effects of these attacks, each one underscoring critical lessons for securing assets in the evolving landscape of cryptocurrency. Here’s a look at some of the most notorious wallet drainers and what they reveal about protecting your digital assets.
1. The Euler Finance Exploit
Loss: Approximately $197 million
Date: March 2023
Type of Attack: Flash loan and smart contract vulnerability

In March 2023, Euler Finance, a DeFi protocol on Ethereum, suffered one of the largest wallet-draining incidents in recent memory. Attackers leveraged a vulnerability in Euler’s smart contracts, initiating flash loans that allowed them to extract funds rapidly from the protocol. This attack showcased the severe consequences that can result from even a single smart contract vulnerability, with assets worth nearly $200 million lost to the exploit.
Lesson Learned:
- Smart Contract Audits: This exploit emphasizes the need for rigorous smart contract security in DeFi, particularly in protocols dealing with large amounts of user funds. Ensuring contracts undergo regular, thorough audits can minimize risks.
- Flash Loan Risks: Flash loans are powerful tools but can be used maliciously to exploit vulnerable contracts, making it essential for platforms to assess and manage flash loan exposure.
2. The Ronin Network Hack
Loss: Approximately $625 million
Date: March 2022
Type of Attack: Private key compromise and validator access

The Ronin Network, the Ethereum-linked blockchain supporting the popular NFT game Axie Infinity, experienced one of the most significant crypto wallet drains to date. Hackers compromised private keys belonging to Ronin’s validators, gaining unauthorized access and approving fake withdrawal requests. The attackers drained $625 million in Ethereum and USDC, which shook the blockchain gaming and DeFi worlds.
Lesson Learned:
- Decentralized Validator Systems: The Ronin incident showed how critical it is for validator networks to use decentralized and multi-layered security protocols.
- Private Key Management: Ensuring the security of private keys is vital, and using multi-signature setups can help protect against single points of failure.
3. The Beanstalk Farms Flash Loan Attack
Loss: Approximately $182 million
Date: April 2022
Type of Attack: Flash loan and governance exploit

Beanstalk Farms, a DeFi stablecoin protocol, was drained of around $182 million through a flash loan attack that manipulated its governance system. The attacker used a flash loan to gain a majority vote in Beanstalk’s governance system, then passed a malicious proposal to transfer assets to an unauthorized address. This complex attack highlighted the vulnerabilities within decentralized governance structures and how quickly they can be exploited by someone with enough resources.
Lesson Learned:
- Governance Security: Protocols must secure their governance systems against large-scale manipulation. Adding time locks or multisig requirements for high-stakes proposals could provide an additional layer of defense.
- Flash Loan Management: Platforms using flash loans should implement safeguards against flash loan-based governance attacks to prevent malicious voting.
4. The BadgerDAO Phishing Attack
Loss: Approximately $120 million
Date: December 2021
Type of Attack: Phishing and frontend compromise

BadgerDAO, a DeFi platform focused on bringing Bitcoin to DeFi, was targeted in a phishing attack where hackers manipulated the platform’s frontend. By embedding malicious code on the website, attackers tricked users into approving transfers from their wallets, ultimately siphoning approximately $120 million. This incident underscored the risk of frontend phishing attacks even on well-established platforms.
Lesson Learned:
- Frontend Security: Even if smart contracts are secure, ensuring the frontend interface is secure is essential to protect user assets. Regular audits and monitoring can help detect suspicious changes in the frontend.
- Approval Caution: Users should be cautious when approving transactions, especially if prompted unexpectedly. Verifying URLs and only interacting with known, secure platforms is critical.
5. The Nomad Bridge Hack
Loss: Approximately $190 million
Date: August 2022
Type of Attack: Cross-chain bridge vulnerability
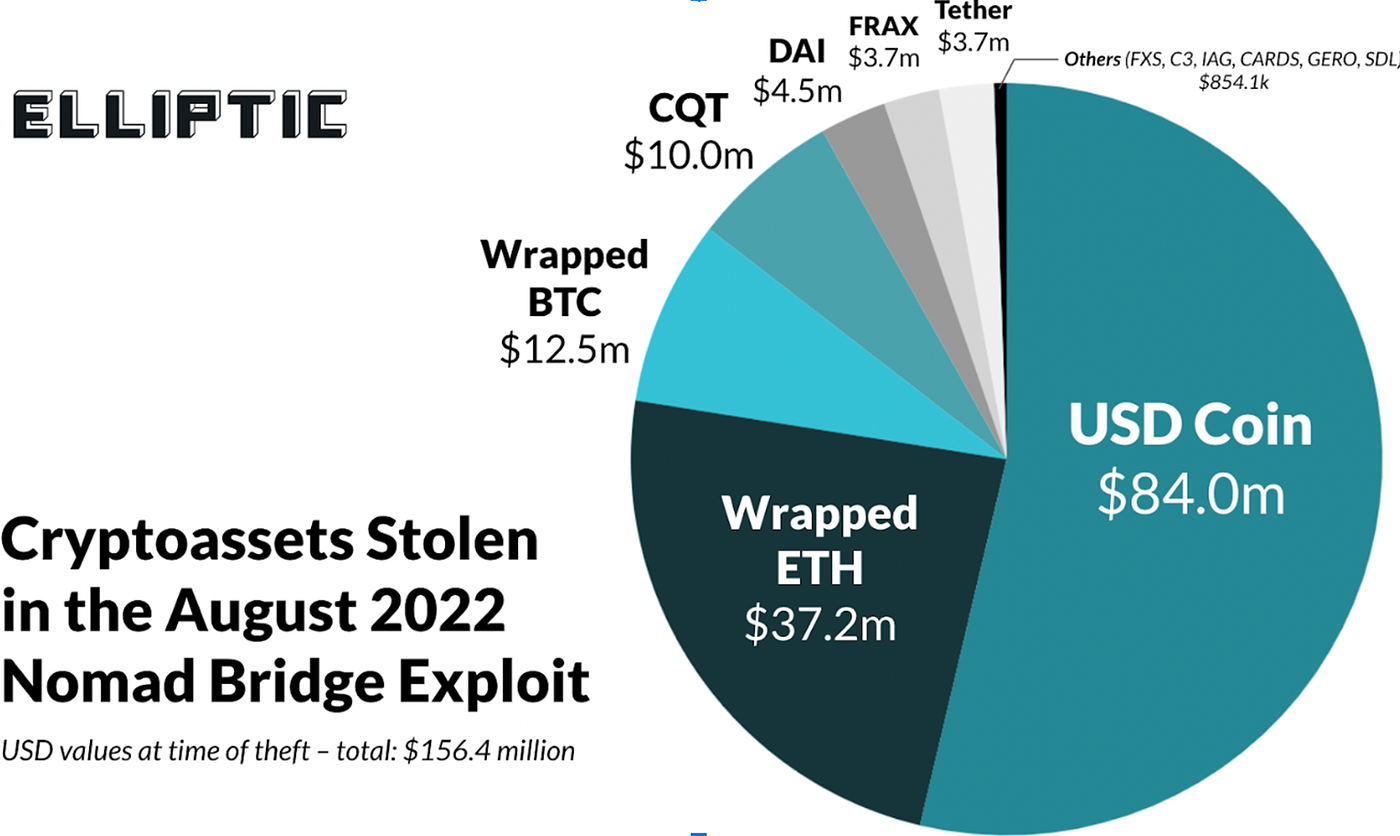
In August 2022, Nomad, a cross-chain bridge protocol, was hacked due to a flaw in its code, allowing users to drain the bridge of $190 million. The Nomad hack gained attention because it was essentially open to anyone who noticed the vulnerability — dozens of opportunistic users quickly joined the attack and drained funds for themselves. This incident revealed the unique security risks associated with cross-chain bridges, which often hold vast amounts of user assets.
Lesson Learned:
- Bridge Protocol Security: Cross-chain bridges are complex and require specialized security measures, including extensive code review and testing. Any error can be costly.
- Code Transparency: Security vulnerabilities in public codebases need rapid responses. Regular monitoring and maintenance are essential to avoid exploits.
6. Harmony Bridge Exploit
Loss: Approximately $100 million
Date: June 2022
Type of Attack: Private key compromise

The Harmony blockchain bridge to Ethereum was breached in June 2022, resulting in a $100 million loss. The attackers gained access through private keys linked to the bridge, allowing them to transfer funds out. This breach showed how vulnerable cross-chain bridges are to security flaws in private key management, especially when handling massive amounts of user funds.
Lesson Learned:
- Enhanced Key Management: Private keys for bridge protocols should be stored and managed with the highest security standards, using multisig and offline storage methods.
- Bridge Security: Like other cross-chain bridges, Harmony’s exploit highlights the need for layered security to prevent similar attacks in the future.
7. The AnubisDAO Rug Pull
Loss: Approximately $60 million
Date: October 2021
Type of Attack: Rug pull and trust exploitation

AnubisDAO, an OlympusDAO fork, pulled off a $60 million rug pull shortly after its token launch in October 2021. Users who had invested in the project lost their funds as developers abandoned the project without notice. This was a “soft drain” rather than a direct hack, as the developers or insiders simply took the funds without fulfilling project promises.
Lesson Learned:
- Due Diligence: Rug pulls highlight the importance of researching projects thoroughly before investing, especially with newer projects.
- Token and Team Transparency: Investors should look for projects with transparent, identifiable teams and audited smart contracts to reduce the risk of similar attacks.
Key Takeaways from These High-Profile Wallet Drainers
These cases each provide unique insights into the tactics of cybercriminals and the potential weak points in digital asset protocols. They underscore several core principles for anyone looking to secure their assets in the crypto space:
- Thorough Smart Contract Audits: Security audits and code reviews are essential for any project handling large volumes of assets.
- Governance Safeguards: Ensuring that governance systems are protected from large-scale manipulation, particularly from flash loans, is crucial for decentralized protocols.
- Frontend and Phishing Protection: Platforms must secure their user interfaces and educate users about phishing risks, as attackers often exploit user trust in the frontend to steal assets.
- Private Key Management: Proper key storage, multisignature setups, and secure validator management are critical in preventing attackers from gaining control over funds.
- Bridge Security: Cross-chain protocols face unique security challenges, requiring specialized audits, code reviews, and key management.
Each of these attacks serves as a reminder of the constant vigilance required to operate securely in the cryptocurrency space. By learning from these high-profile incidents, users and developers alike can better protect their assets and create a safer environment in the evolving world of decentralized finance.
Check out our Medium article here
21 Comments
Alvin4918
27 May 2025https://shorturl.fm/a0B2m
Annabelle4001
28 May 2025https://shorturl.fm/A5ni8
Veronica2060
28 May 2025https://shorturl.fm/a0B2m
Emery3413
28 May 2025https://shorturl.fm/68Y8V
Anna725
29 May 2025https://shorturl.fm/m8ueY
Logan4427
29 May 2025https://shorturl.fm/YvSxU
Lucia2792
29 May 2025https://shorturl.fm/TbTre
Mitchell3320
29 May 2025https://shorturl.fm/YvSxU
KingPH
29 May 2025Understanding the thrill of gambling requires balancing risk and reward – something platforms like KingPH login seem to master with their royal-grade casino experiences and engaging slot adventures.
Damon2831
30 May 2025https://shorturl.fm/68Y8V
Paul1531
30 May 2025https://shorturl.fm/j3kEj
Jeremiah4723
30 May 2025https://shorturl.fm/uyMvT
Ryan1112
30 May 2025https://shorturl.fm/TDuGJ
Gavin227
31 May 2025https://shorturl.fm/xlGWd
Lucia3053
31 May 2025https://shorturl.fm/0EtO1
Billie1443
01 Jun 2025https://shorturl.fm/fSv4z
Manuel1677
01 Jun 2025https://shorturl.fm/0EtO1
Caitlin4649
01 Jun 2025https://shorturl.fm/retLL
Alma1951
01 Jun 2025https://shorturl.fm/MVjF1
Darren1292
01 Jun 2025https://shorturl.fm/retLL
Katie3547
02 Jun 2025https://shorturl.fm/IPXDm